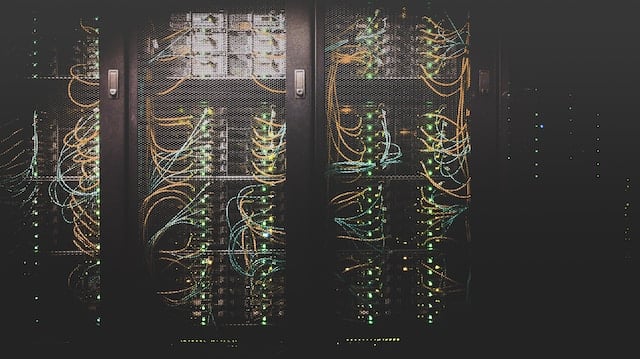
Leave Your IT
Best-in-class IT support for
Industries We Serve
Healthcare
Our security-first approach ensures uninterrupted network performance and top-tier security, facilitating safe and efficient data transfer in healthcare.
Financial
We offer secure data management and communication solutions for the financial sector, ensuring compliance and efficiency for banks, credit unions, and other institutions.
Retail
Our secure SD-WAN and cybersecurity solutions robustly protect retail businesses' sensitive data, enhancing network safety and integrity.
Industrial
Our managed services bolster the automated, IoT-heavy industrial sector with top cloud security and continuous monitoring for seamless business operations.
Oil & Gas
Our solutions offer oil and gas companies robust, always-on technology with 24/7 monitoring and secure cloud infrastructure, minimizing downtime and costs.
SMB
Our cybersecurity, cloud, and network solutions safeguard small to medium-sized businesses, a frequent target for cybercriminals, while supporting growth.
Why Choose Meriplex?

Meriplex has aligned with many of the most innovative technology leaders to build strategies that enhance business growth and scalability. Leading security technology allows us to stay on top of rising threats and challenges and the additional technology investments you make today to further position your company for operational excellence in the future.

As a managed services provider focused on IT strategy and security, we serve as a trusted partner for our customers nationwide. We use a consultative approach to design your solutions with you every step of the way. Rather than simply implementing technologies, we spend time learning about your business requirements to build solutions that provide long-term value.
Related Resources
Essential Guides, Insights, and Case Studies for IT Solutions

Cyber Security
Understanding the Change Healthcare Cyber Attack: Implications for the Healthcare Industry and Beyond
The cyber attack on Change Healthcare underscores the urgent need for enhanced cybersecurity in the healthcare industry after disrupting services and prompting a $20 million ransom demand.
Cyber Security
What Is IT Virtualization?
Virtualization is a powerful IT service that optimizes your physical server by creating multiple virtual machines. Learn more about how it works from Meriplex.

Cyber Security
Cybersecurity for Healthcare: Protecting Patient Data in a Digital World
The healthcare industry is a huge target for cybercriminals. This article will review cybersecurity for healthcare and how to protect PHI in a digital world.

Cyber Security
The Role of Artificial Intelligence in Cybersecurity
AI is playing a major role in every business looking to automate activities. This article will review the role of artificial intelligence in Cybersecurity.

Cyber Security
Zero Trust Security: Redefining Network Security for the Digital Age
The Digital Age calls for increased cybersecurity. This article will help you to better understand Zero Trust Security and how it can help fortify your business.
Cyber Security
Remote Work Cybersecurity
Remote workers are here to stay. This article will review remote work cybersecurity and how you can be proactive in preventing cyber attacks.




